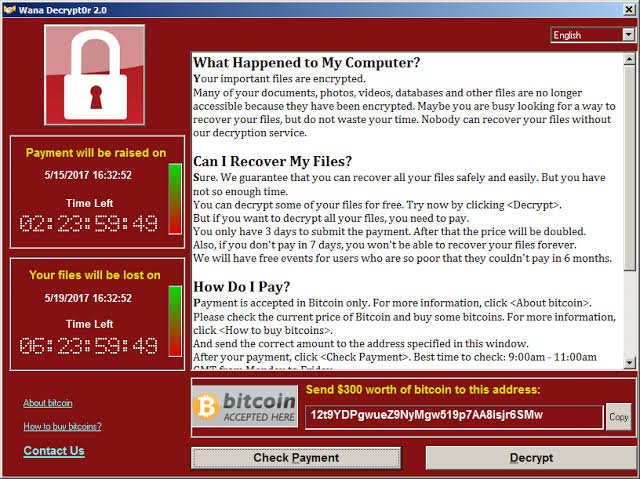
Ransomware attacks are on the rise nowadays. A report suggested that Ransomware alone cost companies up to $20Billion in yearly damages. Cybercriminals that use it are looking to do just one thing- extort your hard-earned money. This usually pops with a notification on your screen which says “ALL YOUR FILES HAVE BEEN ENCRYPTED, write an email to xyx@xyz.com to obtain a decryption key after paying random amount in BitCoins or else your data would be deleted.”
How does it work?
The notification shown above is the end result, but how all of it start? For a Ransomware to start working it follows a lifecycle:
- Click on a malicious link or download a malicious file.
- Ransomware gets activated.
- Files get encrypted.
- Ransom is demanded in form of virtual currency.
- Data is decrypted [very very rare].
Do’s and dont’s to prevent yourselves against Ransomware attacks:
DO backup all your files regularly- manually or automate the process.
DO isolate your device from the network if it is infected with a Ransomware and remove all external devices connected to it.
DO inform your IT department about the attack.
DO have a well-designed Zero Trust Security Policy for your critical resources and the entire network.
DO make sure everything is updated with patches so vulnerable software cannot be tampered with.
DO enable content scanning on your mail server.
DO educate and keep yourself updated with latest threats in the market.
DON’T hand out personal information over email or phone call [phishing]
DON’T click on links in email. Always visit the website from your browser by typing the URL.
DON’T pay ransom to the hacker. This will discourage them to attack as per the FBI.
DON’T download pirated software. Always do it from the manufacturer’s website. Money paid will be far less than damage caused due to cyber-attack.
Unfortunately, Ransomware attacks are going to be there for a long time. This is an easy way to rob individuals and companies alike of their money and not to mention their privacy. The only hope to prevent yourself against it is education and few do’s and dont’s listed above.
True Ransomware protection comes from layered security approach rather than a single point of protection. In simple words, it can be said that the castle should not only be guarded with locks on the main door but to provide protection at each point which may grant access to the castle. Even one point of compromise can cost you the entire castle. Don’t get scared, Stay safe!!
Network Consultant and Trainer by profession with knowledge in multi-vendor environment ranging from routing and switching in Cisco and Juniper to firewalls from Cisco, Palo Alto, Juniper, CheckPoint and Fortigate to virtualization in Cisco UCS and design and deployment of Cisco Viptela SD-WAN solution. Successfully designed and deployed green field and grey field networks for various small to mid-scale organizations.
